To perform explicit SSL bumping with Squid, you need to perform the following steps:
Generate a SSL certificate and key: You can either generate a self-signed certificate or obtain one from a certificate authority. The certificate and key will be used by Squid to encrypt and decrypt the traffic.
Install and configure Squid: Squid is a popular open-source proxy server that can be used to perform explicit SSL bumping. You need to install Squid on the system and configure it to listen on the desired port.
Configure SSL bumping: In the Squid configuration file, enable SSL bumping by adding the following lines:
ssl_bump bump all
ssl_cert_file /path/to/cert.pem
ssl_key_file /path/to/key.pem
Specify the destination servers: In the Squid configuration file, specify the destination servers to which the encrypted traffic will be forwarded. You can also specify a list of domains for which SSL bumping will be performed.
Start Squid: Start Squid with the new configuration. Once started, Squid will begin decrypting and encrypting the SSL/TLS traffic based on the configuration.
Here is an example Squid configuration that demonstrates explicit SSL bumping:
http_port 3128
ssl_bump bump all
ssl_cert_file /path/to/cert.pem
ssl_key_file /path/to/key.pem
acl SSL_ports port 443
acl Safe_ports port 80 # http
acl Safe_ports port 21 # ftp
acl Safe_ports port 443 # https
acl Safe_ports port 70 # gopher
acl Safe_ports port 210 # wais
acl Safe_ports port 1025-65535 # unregistered ports
acl Safe_ports port 280 # http-mgmt
acl Safe_ports port 488 # gss-http
acl Safe_ports port 591 # filemaker
acl Safe_ports port 777 # multiling http
acl CONNECT method CONNECT
http_access allow CONNECT SSL_ports
http_access deny !Safe_ports
http_access deny CONNECT !SSL_ports
always_direct allow all
Bài viết khác
Use AWS to deploy your applications and services
Amazon Web Services (AWS) is a cloud computing platform that provides a wide range of services to help businesses and individuals build and deploy applications in the cloud. AWS offers a variety of services such as compute, storage, databases, networking, security, and more. In this guide, we will walk through the steps to get started […]
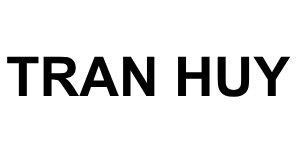
Use docker to run go project
Docker is a powerful tool that enables developers to create, deploy and run applications in a containerized environment. Using Docker to run Go projects has many advantages, including the ability to isolate your application from the underlying operating system, simplifying the deployment process, and allowing for greater scalability and flexibility. In this guide, we will […]
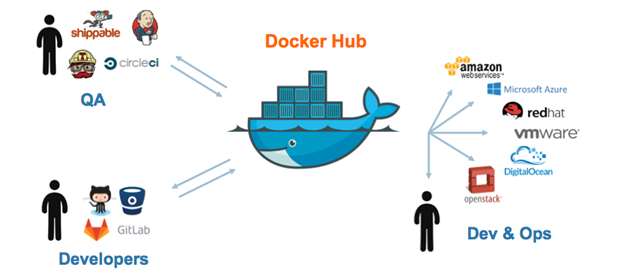
Install WSL for windows 10
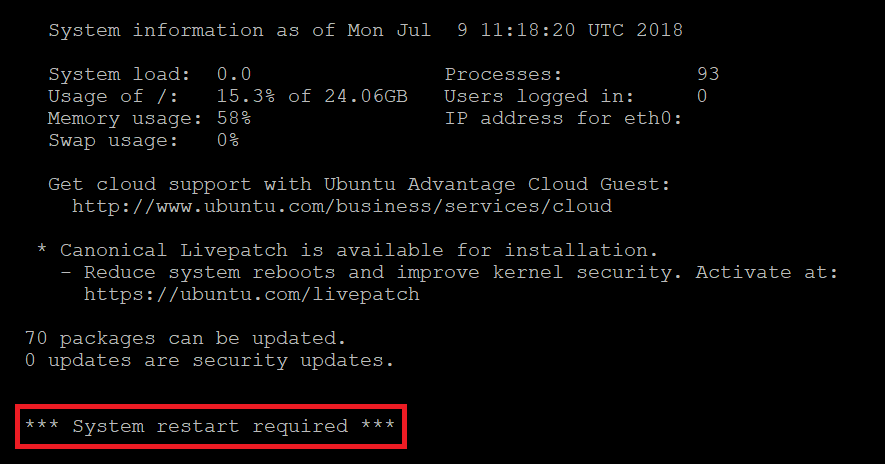
1/ Enable feature Windows Subsystem for Linux Head to Control Panel > Programs > Turn Windows Features On Or Off. Enable the “Windows Subsystem for Linux” option in the list, and then click the “OK” button. Restart computer Now you can type on console: wsl –help 2/ Download ubuntu 18 from Microsoft Store or open […]
Make a binary file or script file run on startup on ubuntu
To make a binary file run on boot, you can create a startup script that will run the binary file when the operating system starts. The exact process for creating a startup script depends on the operating system you’re using. Here’s an example for a Linux operating system using the systemd init system: Create a […]
Explicit ssl bumping with HAProxy
Basic guide About Explicit SSL bumping Explicit SSL bumping also known as “SSL interception,” is a feature of some reverse proxies and security appliances that allows the proxy to decrypt, inspect, and re-encrypt SSL/TLS encrypted traffic. The proxy acts as a man-in-the-middle, decrypting incoming SSL/TLS traffic and re-encrypting it before forwarding it to the destination […]
Nodes and Clusters
It is best practice to create clusters with at least three nodes to guarantee reliability and efficiency Every cluster has one master node, which is a unified endpoint within the cluster, and at least two worker nodes Here, we discover some points of nodes and clusters. Let’s begin Nodes and clusters are two of the […]




 Khoá học lập trình game con rắn cho trẻ em
Khoá học lập trình game con rắn cho trẻ em