Basic guide About Explicit SSL bumping
Explicit SSL bumping also known as “SSL interception,” is a feature of some reverse proxies and security appliances that allows the proxy to decrypt, inspect, and re-encrypt SSL/TLS encrypted traffic.
The proxy acts as a man-in-the-middle, decrypting incoming SSL/TLS traffic and re-encrypting it before forwarding it to the destination server. This allows the proxy to inspect and filter the encrypted traffic based on various security policies, such as filtering out malicious traffic, monitoring and controlling data transfers, and enforcing content filtering.
Explicit SSL bumping is typically used in enterprise networks to provide additional security and control over network traffic. However, it can also introduce security risks and violate the privacy of encrypted communication. It’s important to carefully consider the use of explicit SSL bumping and weigh the security benefits against the privacy risks before deploying it in a network.
To enable SSL bump in HAProxy, follow these steps:
Obtain a SSL certificate and key. You can either generate a self-signed certificate or obtain one from a certificate authority.
Create a new HAProxy frontend and backend configuration. In the frontend configuration, specify the SSL certificate and key with the crt and key options, and enable SSL by using the ssl option. In the backend configuration, specify the target servers to which HAProxy will forward requests.
In the frontend configuration, add a reqadd directive to insert a header indicating that SSL bumping is in effect. This header can be used by the backend servers to determine if a request has been SSL-bumped or not.
In the backend configuration, configure the backend servers to validate the header inserted by HAProxy. This can be done by using the http-request set-header directive to add a header indicating that SSL bumping has taken place.
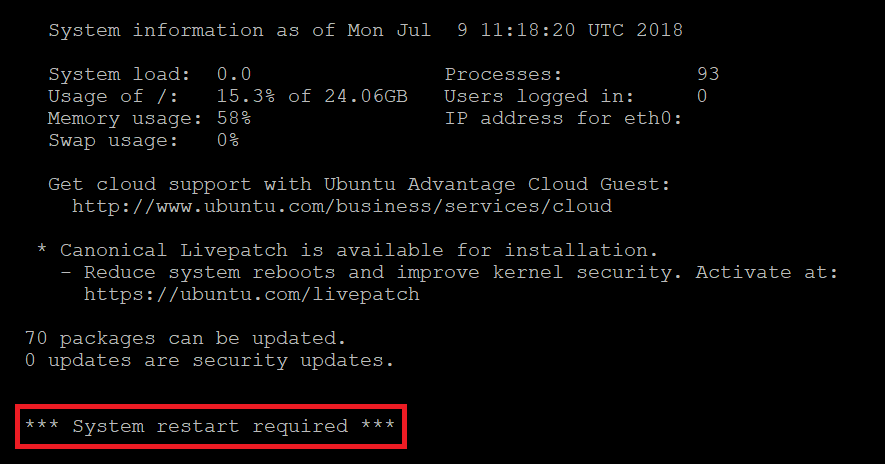
Start or reload HAProxy with the new configuration.
Here’s an example HAProxy configuration that demonstrates SSL bumping:
global
log 127.0.0.1 local0 notice
maxconn 4096
user haproxy
group haproxy
defaults
log global
mode http
option httplog
option dontlognull
retries 3
option redispatch
timeout connect 5000
timeout client 50000
timeout server 50000
frontend http-in
bind *:80
mode http
default_backend servers
frontend https-in
bind *:443 ssl crt /path/to/cert.pem key /path/to/key.pem
mode http
reqadd X-Forwarded-Proto:\ https
default_backend servers
backend servers
mode http
balance roundrobin
server server1 192.168.1.100:80 check
server server2 192.168.1.101:80 check
http-request set-header X-SSL-Bumped true if { hdr(X-Forwarded-Proto) -i https }




 Khoá học lập trình game con rắn cho trẻ em
Khoá học lập trình game con rắn cho trẻ em